What is AppArmor?
AppArmor is a Mandatory Access Control (MAC) framework which is a part of Kernel (LSM) upgrade to keep projects to a restricted arrangement of assets. AppArmor’s security model is to tie access control credits to programs as opposed to clients.
AppArmor repression is given through profiles stacked into the portion, regularly on boot. AppArmor profiles can be in one of two modes: enforcement and complaint.
Profiles stacked in requirement mode will bring about the authorization of the arrangement characterized in the profile just as revealing strategy infringement endeavors (either by means of syslog or auditd).
Profiles in complaint mode won’t implement strategy yet rather report strategy infringement endeavors.
How to check AppArmor Status with aa-status command
To check AppArmor status we use the command aa-status. This command will show the various information like the list of loaded AppArmor module, current AppArmor policy, the command requires sudo to access.
I’ll show you example what we look like when you pass aa-status.
sudo aa-status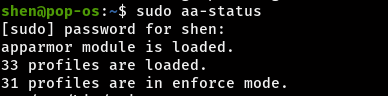
It will show you the first AppArmor module is loaded and 33 profiles are loaded and 31 profiles are in enforce mode.
shen@pop-os:~$ sudo aa-status
[sudo] password for shen:
apparmor module is loaded.
33 profiles are loaded.
31 profiles are in enforce mode.
/usr/bin/evince
/usr/bin/evince-previewer
/usr/bin/evince-previewer//sanitized_helper
/usr/bin/evince-thumbnailer
/usr/bin/evince//sanitized_helper
/usr/bin/lxc-start
/usr/bin/man
/usr/lib/NetworkManager/nm-dhcp-client.action
/usr/lib/NetworkManager/nm-dhcp-helper
/usr/lib/connman/scripts/dhclient-script
/usr/lib/cups/backend/cups-pdf
/usr/sbin/cups-browsed
/usr/sbin/cupsd
/usr/sbin/cupsd//third_party
/usr/sbin/haveged
/usr/sbin/mysqld
/{,usr/}sbin/dhclient
ippusbxd
libreoffice-senddoc
libreoffice-soffice//gpg
libreoffice-xpdfimport
lsb_release
lxc-container-default
lxc-container-default-cgns
lxc-container-default-with-mounting
lxc-container-default-with-nesting
man_filter
man_groff
nvidia_modprobe
nvidia_modprobe//kmod
tcpdump
2 profiles are in complain mode.
libreoffice-oopslash
libreoffice-soffice
0 profiles are in kill mode.
0 profiles are in unconfined mode.
3 processes have profiles defined.
3 processes are in enforce mode.
/usr/sbin/cups-browsed (895)
/usr/sbin/cupsd (759)
/usr/sbin/haveged (752)
0 processes are in complain mode.
0 processes are unconfined but have a profile defined.
0 processes are in mixed mode.
0 processes are in kill mode.
It will list down all the process names and number of process, directory. Above you can see it show 0 processes in kill mode, mixed mode, profile defined, and in complain mode.
Read this: Latest:2020 How to Mount and Unmount File System in Linux?
There are many options which you can use with aa-status like –enabled, –profiled, –enforced, –complaining, –kill, –special-unconfined, –verbose, –json, –pretty-jsoon, –help.
If you want to see aa-status in JSON format that also you can achieve by passing command
sudo aa-status --pretty-json Output
{
"version": "2",
"profiles": {
"/usr/bin/evince": "enforce",
"/usr/bin/evince-previewer": "enforce",
"/usr/bin/evince-previewer//sanitized_helper": "enforce",
"/usr/bin/evince-thumbnailer": "enforce",
"/usr/bin/evince//sanitized_helper": "enforce",
"/usr/bin/lxc-start": "enforce",
"/usr/bin/man": "enforce",
"/usr/lib/NetworkManager/nm-dhcp-client.action": "enforce",
"/usr/lib/NetworkManager/nm-dhcp-helper": "enforce",
"/usr/lib/connman/scripts/dhclient-script": "enforce",
"/usr/lib/cups/backend/cups-pdf": "enforce",
"/usr/sbin/cups-browsed": "enforce",
"/usr/sbin/cupsd": "enforce",
"/usr/sbin/cupsd//third_party": "enforce",
"/usr/sbin/haveged": "enforce",
"/usr/sbin/mysqld": "enforce",
"/{,usr/}sbin/dhclient": "enforce",
"ippusbxd": "enforce",
"libreoffice-senddoc": "enforce",
"libreoffice-soffice//gpg": "enforce",
"libreoffice-xpdfimport": "enforce",
"lsb_release": "enforce",
"lxc-container-default": "enforce",
"lxc-container-default-cgns": "enforce",
"lxc-container-default-with-mounting": "enforce",
"lxc-container-default-with-nesting": "enforce",
"man_filter": "enforce",
"man_groff": "enforce",
"nvidia_modprobe": "enforce",
"nvidia_modprobe//kmod": "enforce",
"tcpdump": "enforce",
"libreoffice-oopslash": "complain",
"libreoffice-soffice": "complain"
},
"processes": {
"/usr/bin/less": [{
"profile": "/usr/bin/man",
"pid": "117499",
"status": "enforce"
}],
"/usr/bin/man": [{
"profile": "/usr/bin/man",
"pid": "117489",
"status": "enforce"
}],
"/usr/sbin/cups-browsed": [{
"profile": "/usr/sbin/cups-browsed",
"pid": "895",
"status": "enforce"
}],
"/usr/sbin/cupsd": [{
"profile": "/usr/sbin/cupsd",
"pid": "759",
"status": "enforce"
}],
"/usr/sbin/haveged": [{
"profile": "/usr/sbin/haveged",
"pid": "752",
"status": "enforce"
}]
}
}
Now status is loaded into JSON format, Other options are available to use you can learn more about this go through the man page.