It’s quite common to forget the root account password if you haven’t used it for a long time.
All Linux users are well aware of how a root account is important to manage administrative tasks like creating users and adding users into a sudo group to perform other important system administrative tasks on behalf of root users.
If you are a single user, you may have created a normal user for other purposes and also been added to the sudo group by the installer or manually for administrative tasks, but for some reason, you have self-removed your account from the sudo group and lost root access.
Later, you discover that you don’t even know the root password to revert the changes, and you’re now stuck with your system where you don’t know the password for your root account.
In this scenario, the only option left is to reset the root account password, so let’s see how you can reset the password in Ubuntu 22.04.
Reset root account password in Ubuntu 22.04
Resetting the root account passwords in Ubuntu 22.04 is a very easy and straightforward process. You just need to follow the subsequent steps in the given order.
Boot system into recovery mode
The first step is to boot your system into recovery mode so you can modify boot parameters, which will allow you to set a new password for your root account.
To get into recovery first, you need to power up your system and wait for it to show the grub menu.
If it is directly showing the Ubuntu logo, then you need to restart your system and continue pressing the ‘ESC’ or ‘Shift’ key until it doesn’t take you to the Grub menu.
The same step you can do if you are using Ubuntu on VirtualBox.
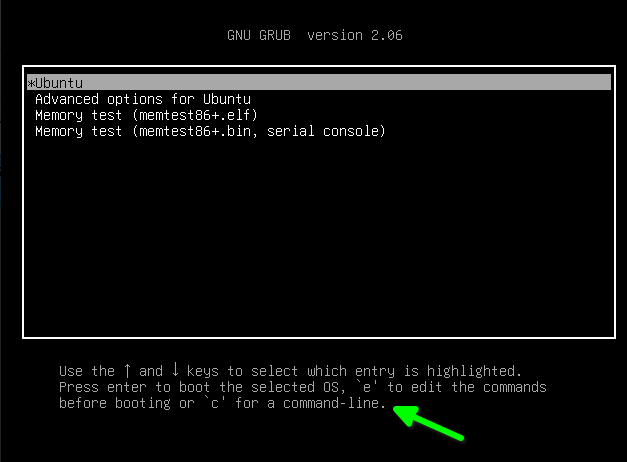
Once you are able to access GNU GRUB, press `e` to modify boot parameters.
Change boot parameters
After pressing `e` on the GNU GRUB menu, you will find the boot parameters like in the below image.
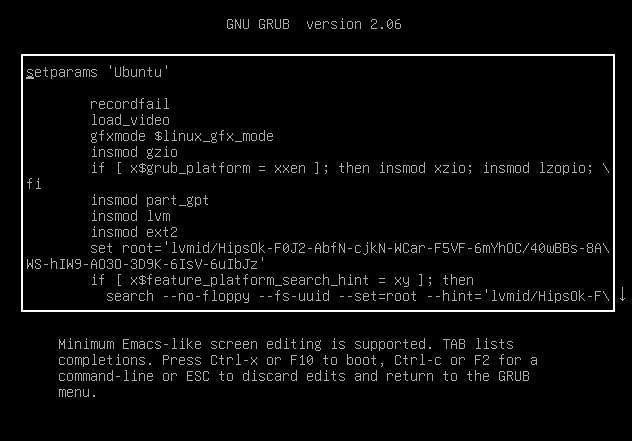
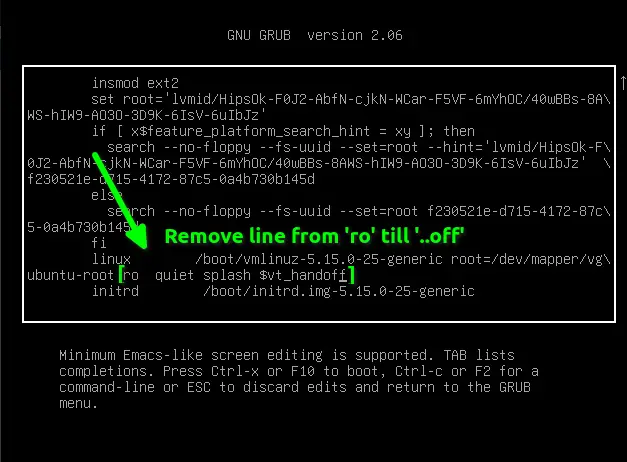
You need to scroll down and find the line where it says "ro quiet splash $vt_handoff", and you have to replace this line of text with "rw init=/bin/bash".
This added line will give you direct access to the root shell with read and write permission.
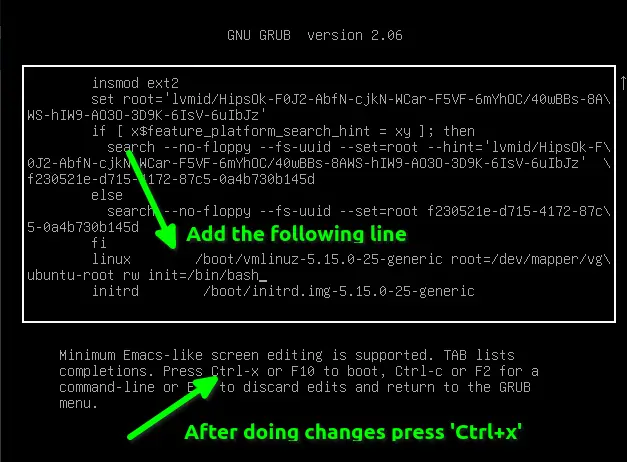
For your reference, I have attached the following image, which you can use to verify changes on your end. If your screen looks like mine, then you need to press “Ctrl + x” or “F10” to boot your system with the following parameters.
After making the above changes, your screen should change, as shown below. Let me clear the screen text by pressing `Ctrl+l`.
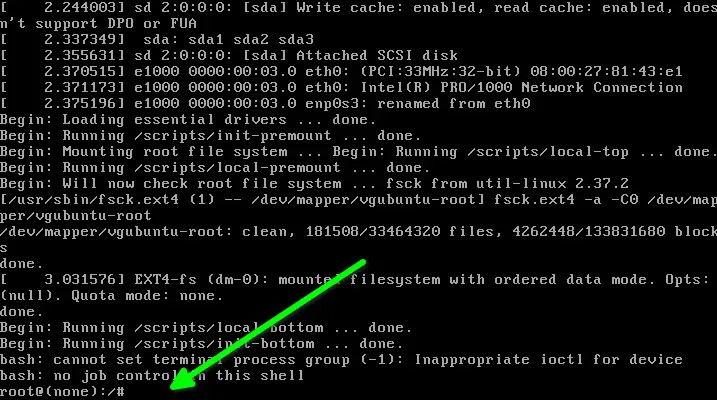
Change the password of your root account
Your root shell is ready to accept input. To reset the root password, type the passwd command, which will ask you to set a new password for your root account.
# passwd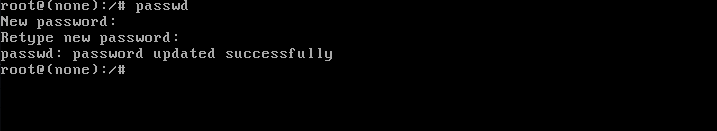
That’s all it takes to reset your root account password. Quite easy, right?
Troubleshooting
If you get an error like “Authentication token manipulation error” which ends up with a “password unchanged” message, then you might have forgotten to boot your system with read and write permission.
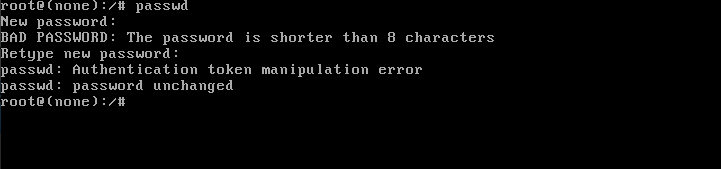
To fix this problem, you can remount your root (/) partition with read and write permissions, which you can easily remount by executing the below code.
# mount -o remount,rw /After that, run the passwd command again to reset the password.
# passwdOnce you are done with the above step, you can restart your computer in normal mode by invoking the below code:
# /sbin/initAfter following the above step, you might think it’s a loophole. If anyone can access my computer data, then how can we say Linux is secure? Yes, I do agree with your concern. The same question arose for me too when I reset the root password for the first time.
Correct, anyone can access your computer through “root shell” or else using “live boot”. To prevent this, you can set a password in the BIOS settings.
After setting up a password, you will find BIOS prompting you to enter a password whenever you try to access your system.
To make it impenetrable, encrypt your disk with some sort of encryption technique, which we’ll cover soon in a separate article.
With that, I’m ending up with this article.